Conforming with the Identification Standards
Use this guidance to learn the types of conformance and the process for getting assessed. Use the tools to gather the evidence needed for assessment.
Types of conformance
Conformance with standards brings consistency and good practice to products and services. It’s a key element to building consumers’ trust in the use of products and services.
There are 3 types of conformance:
Self-assessment
An accountable party, such as a Relying Party, Credential Provider, or Facilitation Provider, can assess themselves against the relevant Identification Standard controls to see if they can meet the requirements. This can be completed without having to commit to a full conformance process.
Qualified assessment
A qualified assessment is useful where there’s no obligation to conform with the Identification Standards or the accountable party is on a journey to conforming and would like to know how close they are.
Qualified assessment is a lighter process than an audited assessment and does not result in a conformance certificate being issued. The assessor will provide advice about the degree to which conformance may be achieved and to what Levels of Assurance.
Audited assessment
An audited assessment is a robust process where evidence, such as documentation and demonstration shows how each of the relevant controls is being complied with.
The length of this assessment process will depend on the degree to which the Identification Standards have already been embedded into the processes being undertaken.
Conformance and mandates
To conform with each of the Identification Standards, ALL the controls will be met.
Voluntary conformance by any party wishing to follow good practice for contributing to the prevention of identity theft and fraud, will be against the levels indicated by undertaking a risk assessment.
Mandated conformance with the Identification Standards is specified through mechanisms such as contracts, cabinet mandates and legislation. The following mandate currently applies:
Conformance with 1 or more of the Identification Standards is a requirement for Digital Identity Services Trust Framework (DISTF) accreditation.
Trust Framework for Digital Identity — Department of Internal Affairs
The conformance process
The formal conformance process occurs in 3 key stages:
- Stage 1 — Introduction and scoping
- Stage 2 — Apply controls and prepare evidence
- Stage 3 — Assessment and certificate issuance.
For help at any point throughout these stages contact the Department of Internal Affairs Identification Team at idmstandards@gdda.govt.nz.
Stage 1 — Introduction and scoping
The first stage of applying the Identification Standards or seeking conformance is to understand which role and standards are relevant.
Understanding identification roles
There are 3 roles when applying the Identification Standards – Relying Party (RP), Credential Provider (CP) and Facilitation Provider (FP).
Most organisations will be a Relying Party at some point in what they do.
Anyone who enrols Entities (people or otherwise) and creates records or accounts for them is a Relying Party.
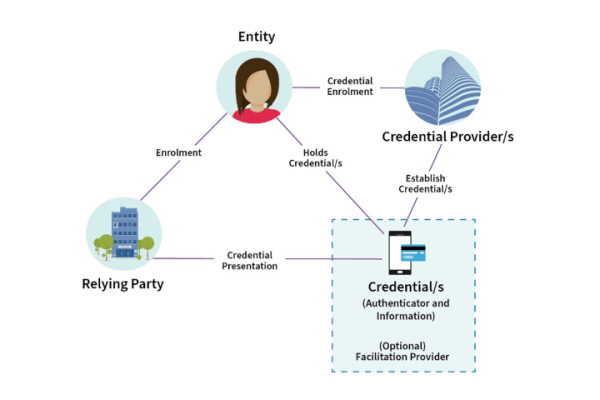
Detailed description of diagram
This diagram depicts how the elements in identification management work together.
An Entity (for example, a person) wants to get a Credential that they can use to get a service from a Relying Party (for example, an organisation). The Entity goes to a Credential Provider to get an applicable Credential and then either presents their Credential directly to the Relying Party or the Credential Provider presents it to the Relying Party for them, sometimes via a Facilitation Provider.
Descriptions of the roles, artefacts and their relationships
- Entity
- An Entity can be a person or machine that presents a Credential to a Relying Party, during enrolment, providing them with assurance that certain identification management processes have been previously carried out.
- Credential
- A Credential is an artefact that’s established for an Entity. It contains an Authenticator and may also have specific information that’s bound to the Entity.
- Relying Party
- A Relying Party provides services to an Entity and requires 1 or more of the Entity’s credentials to establish information about the Entity, to enable provision of the service.
- Credential Provider
- A Credential Provider establishes Credentials for an Entity to present when enrolling with a Relying Party.
- Facilitation Provider
- A Facilitation Provider provides mechanisms for facilitating the presentation of 1 or more Credentials to Relying Parties.
It’s common to hold more than 1 identification role.
- A Credential Provider will also be a Relying Party when they’re enrolling Credential Holders.
- A Credential Provider will also be a Facilitation Provider if they’re involved in the presentation of their Credentials.
- A Facilitation Provider can become a Credential Provider if they create their own Credential.
Understand which standards apply
The identification role and the processes being carried out indicate which of the 5 Identification Standards should be applied.
Table 1 describes the broad identification processes undertaken by each accountable party and the applicable Identification Standards.
| Accountable parties and processes | Applicable standard |
|---|---|
|
Relying Parties enrol Entities by:
|
|
|
Credential Providers:
|
|
|
Facilitation Providers present credentials by:
|
|
|
Authentication Providers:
|
Stage 2 — Apply controls and prepare evidence
The second stage involves applying the individual controls in each relevant standard and gathering the evidence of this.
Risk Assessment
Assessing risk is integral to being able to apply the Identification Standards correctly. Risk assessment determines which Levels of Assurance to apply for certain controls.
While any risk assessment process can be used, more information is available in the following guidance:
Applying the relevant standard controls
Applying the controls in each of the relevant standards is the main part of the journey to conformance.
Meeting certain Levels of Assurance can mean changes need to be made to some systems and processes. These may not be easy or fast to implement. If the planned Levels of Assurance cannot be met, decisions will need to be made about the impact of meeting a lower level of assurance.
If the target Levels of Assurance are unable to be met, options include:
- carrying out additional work to reach the target Levels of Assurance; or
- electing to operate at lower Levels of Assurance.
The latter option does not prevent continuing to work on the aspects that need improvement and seeking reassessment later.
Contact the Identification Team for advice at idmstandards@gdda.govt.nz on different options.
Each of the Identification Standards has an implementation guide which provides more information about how to apply the controls and examples.
Identification Management Guidance
Documenting evidence for assessment
Identification processes may already be well documented. This documentation can be used as evidence for assessment if it’s cross referenced to the relevant controls. Clear descriptions of the functional and operational elements are needed.
Any information that’s not disclosed for the conformance process can be redacted or removed. Alternatively, organisations may wish to extract the relevant information into new documents.
A series of checklists are available to help with collating evidence. They outline the type of evidence that’s needed for each of the relevant controls.
- Information and Binding Assurance conformance checklist (DOCX, 49KB)
- Authentication Assurance conformance checklist (DOCX, 47KB)
- Credential Establishment conformance checklist (DOCX, 44KB)
- Facilitation Mechanisms conformance checklist (DOCX, 49KB)
Documenting conformance with controls that have Levels of Assurance is potentially a new concept. Two additional templates are available to help with documenting Levels of Assurance.
- Information and Binding Levels of Assurance Table template (DOCX, 50KB)
- Authentication Factor Level Table template (DOCX, 44KB)
You do not need to have all documentation complete for assessment to commence. Documents can be sent progressively, for early feedback on progress.
Stage 3 — Assessment and certificate issuance
The third stage involves the steps to get assessed and the outcomes from this process.
If a self-assessment is being undertaken, this stage is not needed.
Deciding on a qualified or audited assessment
The type of assessment being undertaken impacts both the duration of the assessment phase and what’s produced at the end of it. The options are:
- qualified assessment — lighter process that results in informal advice about the degree to which conformance may be achieved and to what Levels of Assurance
- audited assessment — robust process that includes a demonstration and results in an Identification Standards Conformance Certificate.
Schedule an assessment
Contact the Identification Team at idmstandards@gdda.govt.nz to schedule the assessment.
The assessment process involves:
Submitting evidence for review
This evidence will include the completed checklists and associated documents that describe how the controls are being met. Submitting evidence can be done progressively. The assessor will review the evidence as it is submitted.
Responding to requests for additional information
The assessor may require additional information about the identification service or services being assessed or may need further evidence about the controls and levels of assurance.
Doing a demonstration
To confirm that the identification processes within a product or service operate according to the documentation provided the assessor will request a physical demonstration.
Assessment outcome
At the end of the assessment process the organisation being assessed will have an opportunity to discuss the assessment before 1 of the following final documents is issued.
Advice
For a Qualified assessment, the Identification Team will provide written advice. The advice is not evidence that the identification service or services conform with the standards, but it will indicate how close they’re to conforming, and to what Level of Assurance.
Certificate
Following a successful Audited assessment, an Identification Standards Conformance Certificate will be issued. The conformance certificate will describe:
- the organisation
- the identification service or services provided
- the standards conformed with
- the Levels of Assurance expressions for any assured information or authenticators
- the expiry date of the certificate.
With permission, aspects of the certificate may be published on a public register for others seeking to verify the certificate.
Re-conformance
Both advice and conformance certificate are issued at a point in time. There are several things that may make it necessary to apply for re-conformance:
Certificate expiry
Certificates are only issued for a maximum of 3 years. The Identification Team will advise when expiry is due and arrange for re-conformance. The size of the assessment will depend on whether any changes have been made since the original certificate was issued.
Change made to a product or service
If a change is made to the product or service that was assessed, it may no longer be conformant. A new assessment can be carried out on the aspects that have changed.
Changes to the Identification Standards
The Identification Standards will change from time to time to remain relevant. In some cases, a change may result in the need for re-conformation before the expiry of a certificate. Conforming parties will be consulted well in advance should this occur.
Outcome of a complaint
If the Identification Team receives a complaint about a service or product that brings into question whether it’s conformant, an investigation will be carried out. Should the outcome of the investigation impact the status of a certificate, re-conformance may be required to retain a valid certificate.
We’re here to help
For all enquiries, requests, and assessment booking, please contact the Identification Team at the Government Digital Delivery Agency (GDDA) at idmstandards@gdda.govt.nz.
In addition to advice on conformance, we can also help with the following aspects:
- Reviewing identification risk assessments and suggesting improvements
- Interpreting and applying the Identification Standard controls
- Suggesting alternative ways to design processes
- Advising on options if controls cannot be met.
The Identification Team also provides training and clinics to help develop identification capability.
